AutomationDevSecOpsDataOpsGenAILLMOps
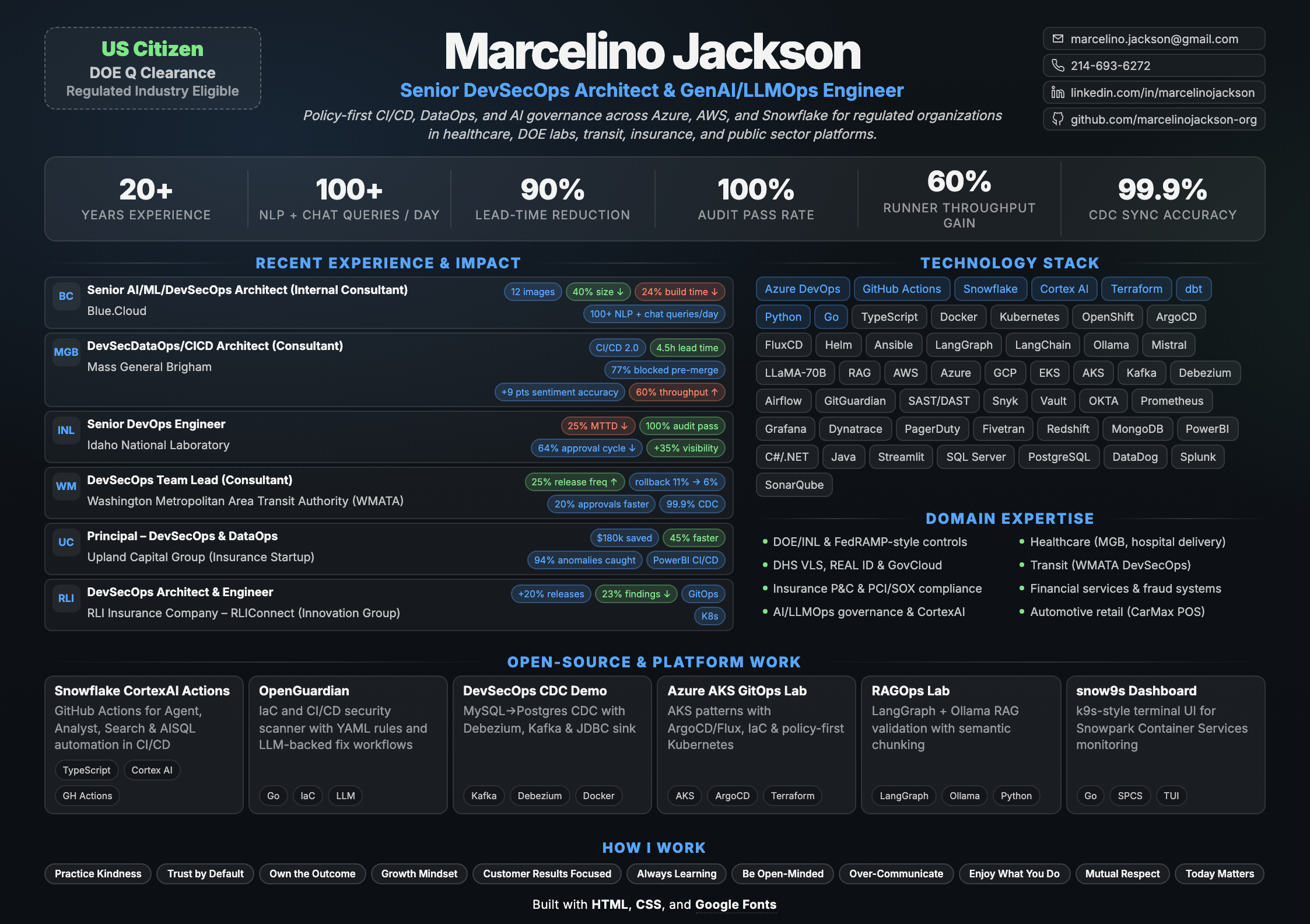
Marcelino Jackson
Senior DevSecOps, Data & AI Platform Architect
Senior DevSecOps, DataOps, and AI/Platform Architect with 20+ years delivering secure, automated platforms in regulated sectors including nuclear, government, insurance, airlines, healthcare, transit, and DOE labs. I translate executive strategy into production systems, operating models, and measurable outcomes — delivering policy-first CI/CD, sovereign and air-gapped AI platforms, secure IaC, and data and AI pipelines across Azure, AWS, and Snowflake, with recent wins in CortexAI governance, CI/CD 2.0 modernization, multi-LLM guardrails, Mistral tuning, and AIOps self-healing.
US Citizen with previously held Secret "Q" Dept-of-Energy (DOE) Clearance
Fully Remote
Collaboration
Ownership
Growth
Regulated healthcare & public sector
- Delivered DOE-compliant CI/CD controls and audit-ready release governance while maintaining delivery velocity.
- Built Azure DevOps observability and on-prem LLM/AIOps pipelines for INL with measurable MTTD and incident triage improvements.
- Led CI/CD 2.0 and CortexAI governance modernization for Mass General Brigham with policy-as-code and secure AI workflows.
- Directed public-sector modernization patterns across transit and DMV platforms under strict compliance expectations.
Insurance & financial services
- Modernized cloud data platforms for Upland and RLI using Terraform GitOps, dbt/Snowflake governance, and secure release automation.
- Reduced integration and identity friction with OKTA + Snowflake + Salesforce patterns across insurance programs.
- Drove enterprise modernization roadmaps tied to CIO/Board outcomes, compliance, and measurable delivery improvements.
Transportation & consumer services
- Shipped DevSecOps modernization at WMATA, increasing release frequency and reducing rollback risk.
- Delivered national-scale payments and integration modernization at CarMax with PCI/SOX-aligned release discipline.
- Supported airline and transportation fraud/payment systems with modernization, data integrity, and secure operations.
AI/LLMOps governance
- Implemented CortexAI multi-LLM governance, RAG validation, and policy-as-code guardrails in CI/CD workflows.
- Applied Mistral fine-tuning and human-in-the-loop practices for higher-quality sentiment and triage outcomes.
- Operationalized AI-assisted DevSecOps patterns across Snowflake, Azure, AWS, and on-prem environments.
Crossing Over: We Forgot How to See Each Other
"A reflection on empathy, division, and rebuilding human connection"
Personal perspective on how polarization erodes understanding and what it takes to see each other again.
Agents.md: The Wachowskis Warned Us
"Why agent design needs guardrails, context discipline, and human oversight"
Perspective on agentic systems, control boundaries, and practical design lessons through a cultural lens.
Maslow, Monks, and the Steam Room That Humbled Me
"Lessons in humility, wellness, and what really matters"
Personal reflection on growth, humility, and finding perspective outside of work.
Shipping AI-Powered Snowflake Workflows with GitHub Actions
"How I built reusable CI/CD patterns for AI-powered Snowflake workflows"
Technical guide on integrating Snowflake CortexAI with GitHub Actions for automated, governed data pipelines.
Shift Left in Practice: SAST, DAST, and SCA with GitHub Actions
"Building auditable security workflows with Snyk, ZAP, and Trivy"
Integrating automated security gates for safer deployments in modern DevOps pipelines.
100% Coverage, 0% Confidence
"Why scan coverage alone does not guarantee security confidence"
OpenGuardian-focused walkthrough on validating findings quality, reducing false confidence, and tightening remediation workflows.
4011
"A reminder that empathy and usability matter as much as implementation"
Reflection on user experience blind spots, ownership, and what changes when you become the user of your own system.
Imposter at the Velvet Rope: A Senior Engineer's Guide to Singleton Survival
"Navigating senior roles when you feel like the only expert in the room"
Professional growth, leadership, and overcoming imposter syndrome as a senior technical leader.
My AI Talked to Your AI and Neither of Us Care
"The reality of LLM-to-LLM automation and keeping the human element in IT"
Reflections on LLMs, automation plumbing, and why humans still matter in the loop.
Non-PROD Deployments and the Fellowship of Canines
"Infrastructure management lessons with humor and a cast of canine advisors"
A lighter take on deployment pipelines, testing, and the dogs who keep you sane.
Distracting Away the Depression
"Mental health transparency from a tech leader's perspective"
A personal essay on distraction, restlessness, and making space for silence.
Led and built Snowflake-based GenAI and data platform delivery for regulated clients, combining self-service analytics, governed access, and multi-cloud build optimization with measurable gains.
Experience
- Multi-cloud releases were slowed by a fragmented container build process. Consolidated it into a single multi-stage pipeline producing 12 Linux images, cutting image size by 40% and build time by 24%.
- Roadmap execution was inconsistent across a distributed engineering team. Introduced architecture reviews and code quality standards to operationalize GitOps delivery, improving on-time milestone delivery from 64% to 91%.
- Business users were blocked on developers for ad hoc SQL requests. Launched a self-service Snowflake Intelligence layer (Cortex Agents, Analyst, Search) handling 100+ daily NLP + chat queries and removing 18 developer hours/week from request queues.
- AISQL workflows had governance gaps that increased exposure risk in a production Snowflake tenant. Implemented RBAC and dual-control access policies, raising governed coverage to 96% and reducing policy exceptions by 57%.
- Profitability planning lacked machine-level forecasting by ship and voyage. Led a Snowflake ML + Cortex AI POC that achieved 86% forecast accuracy and improved pilot-route margin by 8%.
Led Azure DevSecOps, DataOps, GenAI, and LLMOps modernization across Azure DevOps, Snowflake, and dbt with policy-first CI/CD and AI-governed data pipelines.
Experience
- Deployments across Azure DevOps and Snowflake were taking 1.8 days end-to-end. Rolled out CI/CD 2.0 with Policy-as-Code guardrails, cutting median lead time to 4.5 hours (90% faster).
- CI/CD 2.0 adoption was inconsistent across teams. Ran lunch-and-learns plus implementation guides that onboarded 16 engineers across 3 squads and reduced time-to-first-production deployment by 38%.
- Critical dbt/SQL compliance issues were escaping into late review stages. Implemented CortexAI multi-LLM governance with automated PR feedback, blocking 77% of critical non-compliant patterns pre-merge during POC validation.
- Sentiment modeling quality was limited and labeling effort was too manual. Fine-tuned Mistral 7B on anonymized clinical feedback with human-in-the-loop sampling, improving accuracy by 9% and reducing labeling effort by 30%.
- Patient issue trends were difficult to detect quickly in existing reporting. Deployed real-time interactive sentiment dashboards that helped leadership prioritize fixes and resolve critical patient-facing issues 40% faster.
- Code reviews were slowed by noisy semantic checks on dbt changes. Added RAG-based validation in CortexAI against business documentation, reducing false-positive review alerts by 52%.
- Security controls were manually rolled out, creating deployment friction and governance lag. Automated Snowflake RLS/CLS via Terraform CI/CD, achieving 100% policy-as-code coverage and cutting control rollout from about 2 days to 35 minutes.
- Build queues and runner saturation were constraining delivery speed. Scaled Azure DevOps agent pools using OpenShift and AWS-hosted runners, improving build reliability to 89% and increasing concurrent pipeline throughput by 60%.
- Python dependency resolution was adding avoidable delay to pipeline runs. Migrated dependency management to UV, improving overall build efficiency by 62%.
- Failed builds required frequent manual re-runs and extended recovery cycles. Added AIOps-driven self-healing feedback loops, reducing manual re-runs by 34% and lowering pipeline incident MTTR by 27%.
Combined DevSecOps, DataOps, GenAI, and LLMOps with AIOps observability in a regulated DOE lab environment—modernizing CI/CD, adding governance, and delivering on-prem LLM pipelines.
Experience
- Pipeline failures were discovered too late to prevent delivery delays. Built Azure DevOps observability dashboards with Python + REST APIs, cutting build-failure MTTD by 25% and increasing pipeline visibility by 35%.
- Regulated releases needed stronger control gates without slowing engineering output. Hardened build/release pipelines with DOE-compliant environment controls, sustaining a 100% audit pass rate and zero unauthorized production releases.
- Compliance approvals were slowing security changes and creating release risk. Served as the technical liaison between engineering and DOE compliance teams, reducing security-control approval cycle time from 4 weeks to 10 days (64% faster) without delaying releases.
- Secret detection was inconsistent across repositories and audit exposure remained high. Operationalized PR-triggered GitGuardian onboarding, reducing secret exposure incidents by 45% and lowering audit findings by 29%.
- Hybrid cloud patterns varied by division, creating uneven onboarding. Defined Azure/AWS architecture standards adopted by 3 internal divisions, reducing platform onboarding time for new teams by 35%.
- Legacy scheduler replacement options were unclear and template creation was slow. Ran Airflow, n8n, and Apache NiFi POCs with local-LLM-generated Terraform/Ansible scaffolds, cutting template authoring time by 45% and producing disposition paths for 100% of targeted workloads.
- TB-scale historical logs were difficult to analyze for early incident patterns. Architected an on-prem LLM pipeline (Ollama + LangGraph + RAG) to automate anomaly detection and accelerate incident triage.
- Load balancer and API gateway changes were manual and drift-prone across a pilot scope. Built a GitOps-backed Terraform platform for Citrix ADC and evaluated Kong API Gateway for DOE-compliant API traffic management, with a Streamlit self-service intake for 3 teams' repositories as a small-subset POC, eliminating manual config drift and reducing infrastructure change lead time from 2 days to 25 minutes (99% faster).
- Troubleshooting required hopping across disconnected operational tools. Unified observability signals across WordPress logging, PagerDuty, and Slack dashboards, reducing troubleshooting time from 3 hours to 25 minutes (86% faster).
Modernized DevSecOps foundations for a large transit organization, aligning tooling, process, and AWS platform choices to accelerate delivery with governance.
Experience
- Delivery tooling differed across teams, increasing operational friction. Built and drove a DevSecOps modernization roadmap adopted by 6 major product teams, standardizing toolchains.
- Frequent rollback risk was limiting deployment confidence. Simplified branching and deployment workflows, increasing release frequency by 25% and reducing production rollback rate from 11% to 6% (45% reduction).
- Cross-division approvals slowed execution and destabilized sprint scope. Aligned agile delivery across business units, reducing leadership approval cycle time from 10 business days to 8 days (20% faster) and improving sprint scope stability by 30%.
- Cloud adoption stalled among legacy administrators and slowed IaC rollout. Led an AWS-first capability shift by mentoring 3 legacy system administrators, increasing IaC-driven change adoption from 28% to 76%.
- Data transformation deployments lacked a consistent release path. Engineered CI/CD-integrated ELT pipelines with AWS Fargate and Azure DevOps, standardizing dbt deployments.
- CDC orchestration across hybrid environments was brittle and hard to scale. Built resilient, parameter-driven Python orchestration patterns, sustaining 99.9% data synchronization accuracy across hybrid AWS and on-prem systems.
- Schema drift was leaking defects downstream into analytics consumers. Implemented automated data quality gates in Snowflake pipelines, detecting schema anomalies pre-production and reducing downstream data defects by 25%.
- Legacy CI tooling increased cost and slowed governance modernization. Led migration from Bamboo to GitHub Enterprise and HashiCorp Vault, completing transition 3 weeks ahead of schedule and reducing annual CI infrastructure costs by 12%.
- API traffic across transit systems relied on disparate, team-specific gateway configurations with no centralized governance. Leveraging previous experience deploying Kong at two startups, authored and presented a Kong adoption proposal and proof-of-concept for centralized API management, defining gateway-as-code practices, plugin standards, and a phased rollout plan for adoption by downstream product teams.
Built greenfield DevSecOps and DataOps for analytics and applications using dbt/Snowflake, GitHub Actions, Terraform, and SSO.
Experience
- PowerBI release processes relied on manual steps and expensive licensing paths. Built a custom PowerBI CI/CD framework via CLI and Microsoft Graph, avoiding $180K/year in premium licensing costs while cutting report onboarding time by 35%.
- Identity and integration friction was slowing analytics access. Standardized OKTA SSO and Snowflake-Salesforce integrations through Kong Gateway's OAuth2/OIDC plugins and governed dbt models, centralizing auth enforcement and reducing login issues by 28% and data sync latency by 30%.
- Snowflake environment setup was slow and drift-prone. Automated RBAC, warehouses, and schemas through Terraform-driven GitOps, reducing environment provisioning time by 45% and cutting configuration-drift incidents by 90%.
- Hybrid cloud data throughput and availability were below business targets. Co-authored the AWS/Azure hybrid data strategy across Snowflake, dbt Core, and Fivetran, increasing pipeline throughput by 26% and data availability by 15%.
- Vendor data ingestion was creating delays for downstream analytics. Streamlined ELT pipelines with Fivetran and Python-wrapped dbt workflows, accelerating external vendor-feed ingestion by 40%.
- CDC deployments required repeat custom work across environments. Designed parameterized orchestration templates, sustaining 99.9% execution reliability and reducing deployment rework by 32%.
- Critical data anomalies were reaching production dashboards before detection. Built SQL-based lineage and reconciliation validation suites, detecting 94% of critical data anomalies before they reached production dashboards.
- Freshness and schema-change impacts were hard to detect quickly. Implemented data observability across dbt models and Snowflake schemas, improving freshness transparency and reducing schema-change time-to-fix by 50%.
- Platform modernization funding required executive alignment and a clear roadmap. Authored and presented a 3-year DevSecOps strategy to the CIO and Board, securing modernization funding approval and pulling phase-one delivery forward by one quarter.
- CRM and data platform releases were colliding in delivery windows. Established the Salesforce DevOps Center operating cadence, aligning CRM releases with data platform transformations and reducing deployment conflicts by 20%.
- API traffic between cloud services and the hybrid data layer had no unified routing or throttling strategy. Architected Kong API Gateway as the central routing and governance tier between application services (AWS/Azure) and the Snowflake data platform, managing traffic policies with decK declarative configurations and enabling canary-style API versioning during data pipeline migrations.
- External vendor and partner APIs lacked centralized governance, creating inconsistent authentication and unpredictable latency. Deployed Kong API Gateway as the ingress layer for all vendor-facing and Salesforce integrations, implementing OAuth2 and rate-limiting plugins, request/response logging, and API lifecycle versioning — reducing integration failures by 32% and providing full API observability for the first time.
Delivered secure DevSecOps foundations across Azure/AWS and hybrid Kubernetes, standardizing pipelines, security gates, and resilience practices for microservices and data platforms.
Experience
- Microservice delivery lacked a unified multi-cloud release model. Engineered Azure/AWS DevSecOps pipelines with Kong Gateway declarative config (decK) integrated into CI/CD, standardizing API deployment patterns, increasing release frequency by 20% and reducing change failure rates.
- Security checks were inconsistent and often late in the release cycle. Defined and enforced a Security-First deployment stance with automated SAST/DAST gates, reducing production security findings by 23% and accelerating approval cycles by 18%.
- Toolchain gaps and manual CI/CD steps were slowing teams. Developed custom Golang CLI utilities and mentored engineers on GitOps workflows, reducing manual intervention by 30% and shortening developer onboarding time by 25%.
- GitOps adoption was uneven across the organization. Established a Community of Practice and mentored 10+ developers to raise overall cloud maturity.
- Provisioning Kubernetes environments across clouds was slow and inconsistent. Architected a hybrid AKS/EKS/on-prem platform with Ansible and Terraform, reducing environment build times by 40% and enforcing configuration consistency.
- Resilience and data-operations practices were fragmented in critical stores. Institutionalized Chaos Engineering and DataOps for Snowflake and MongoDB, reducing defect escape rates and improving system recovery times by 21%.
- Microservices lacked a unified API gateway, exposing inconsistent routing, authentication, and rate-limiting. Selected and deployed Kong API Gateway (Enterprise) as the centralized ingress layer for the AKS/EKS platform, implementing rate limiting, JWT authentication, request transformation, and custom plugin development — reducing integration onboarding time for new services by 35%.
- Service-to-service communication across the hybrid Kubernetes footprint was ungoverned and difficult to trace. Implemented Kuma Service Mesh alongside Kong Gateway to enforce mTLS, enable distributed tracing via Kong Connect, and provide east-west traffic observability — reducing untracked internal API calls to near-zero and improving incident root-cause identification time by 28%.
- API lifecycle management was ad hoc, with no consistent deprecation, versioning, or consumer-notification process. Established an API lifecycle governance framework using Kong's developer portal, automated API documentation via Swagger/OpenAPI specs, and defined deprecation workflows — improving consumer adoption tracking and reducing breaking-change incidents by 40%.
Led DevSecOps and modernization delivery for insurance claims platforms across cloud and on-prem environments.
- Built self-service Ansible/Bitbucket/Jenkins deployment workflows that enabled zero-touch higher-environment releases and reduced deployment lead times by 60%.
- Standardized cloud and release tooling by consolidating CloudFormation/CodePipeline patterns into Ansible/Terraform, reducing operational cost and configuration drift.
- Delivered mission-critical ClaimsPro deployments with 99.9% reliability across SQL Server and artifact workflows.
- Expanded observability and incident response patterns (Dynatrace, PagerDuty, Slack), reducing MTTR by 40%.
- Modernized identity and fraud workflows through OKTA + LDAPS integrations and real-time analytics patterns.
Directed REAL ID, Verification of Lawful Status, and modernization for DMV services spanning kiosks, .NET stacks, and AWS GovCloud adoption under DHS oversight.
- Architected, coded, and launched REAL ID services for the Driver’s License division, tying on-prem, kiosk, and cloud systems together.
- Built and governed DHS Verification of Lawful Status integrations across three delivery platforms while meeting clearance-driven controls.
- Led .NET/WCF/WPF modernization teams for VLS services, maintaining kiosk software for NCDL/CDL workflows and coordinating legislative enhancements.
- Led medium-to-small legislative compliance projects using VB.NET and PowerBuilder to extend DMV services.
- Authored cross-functional documentation (flowcharts, interface diagrams, ROI briefs) and presented to leadership to secure modernization funding.
- Evaluated AWS GovCloud adoption paths, new tooling, and upgrade plans to keep DMV modernization ahead of compliance mandates.
Led ETL/data-migration heavy initiatives plus internal “Special Projects” modernization, supporting P&C stakeholders and offshore teams.
- Architected and delivered ETL/data migration pipelines from heterogeneous databases into the enterprise warehouse and third-party feeds.
- Managed development/support backlogs, produced technical specs, and shepherded projects from discovery through production for business owners.
- Ran the “Special Projects” modernization assessment, briefing the VP of Applications quarterly on tooling direction, gaps, and ROI.
- Reported modernization progress and ROI to executive leadership while coordinating cross-team delivery milestones.
- Trained and coordinated offshore teams to absorb Level II support and enhancements, ensuring regulated programs stayed on track.
Delivered national point-of-sale initiatives, data feeds, and payments modernization for CarMax retail operations.
- Built and rolled out debit card acceptance for 100+ stores, integrating .NET services with card readers, signature capture, refunds, and QA tooling.
- Built a WPF test app for card reader validation and retrofitted refund workflows that were out of scope in the original design.
- Engineered Jesubi auction data feeds via PowerShell, C#, and XML pipelines that stitched together DW, MongoDB, and SQL Server logic that had never been documented.
- Extracted undocumented business logic and designed seed/incremental feeds to align data delivery with enterprise architecture and security requirements.
- Partnered with enterprise architects, DBAs, and security to document, secure, and deploy every integration, ensuring PCI/SOX alignment.
Long-tenured engineer delivering and modernizing airline systems spanning fraud, finance, travel rules, and internal tooling.
- Led the credit fraud IT team in migrating processes to Accertify, pairing in-house Java services with third-party automation for PCI compliance.
- Rebuilt critical apps from legacy C++/COBOL to Java (Swing/AWT/JSP) and .NET, plus designed extracts/reports when workloads moved to vendors.
- Built feeds, extracts, and reports when legacy systems were outsourced, maintaining data integrity and auditability.
- Supported numerous in-house applications, balancing feature delivery with operational ownership while mentoring teams on secure coding practices.
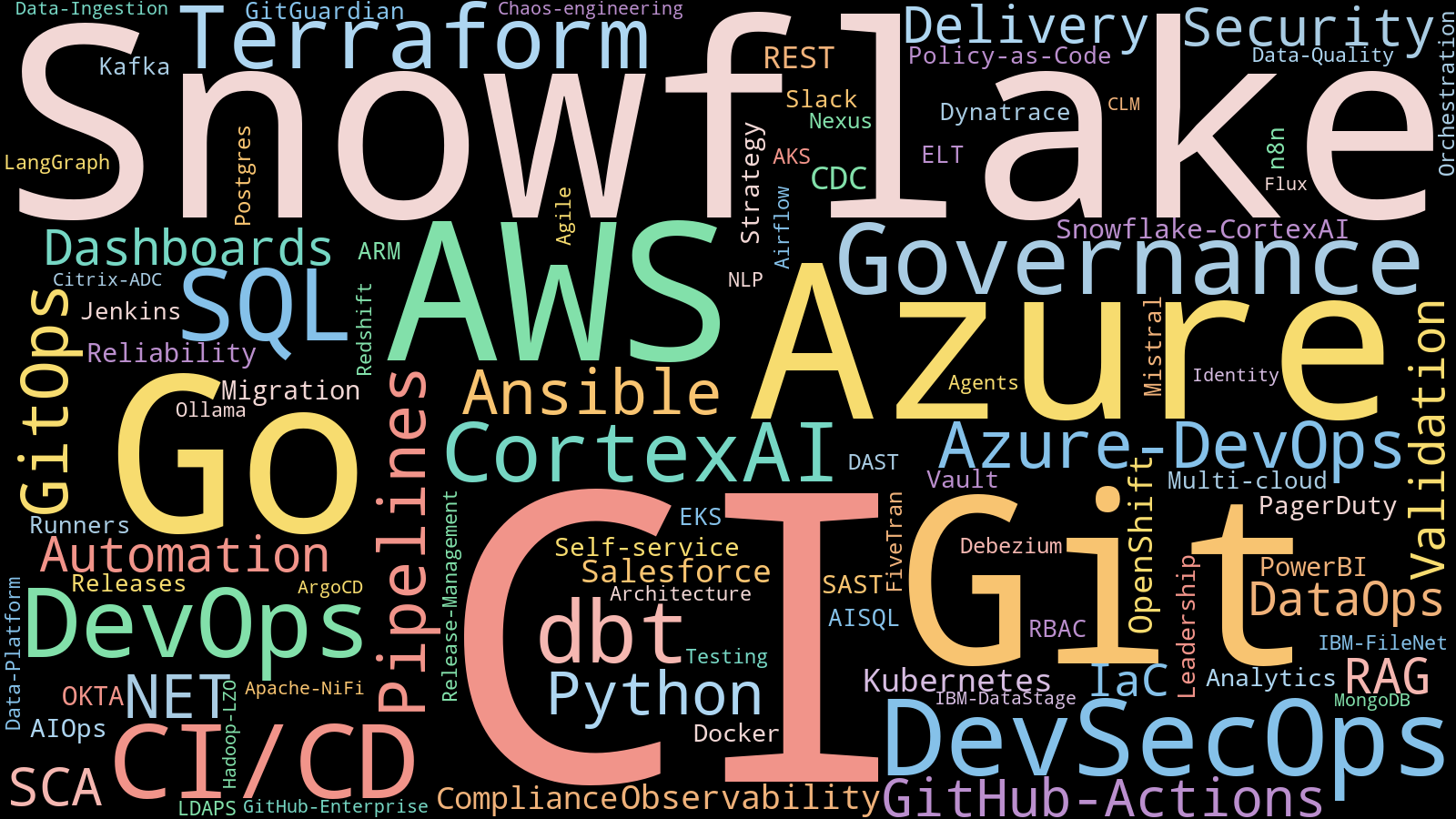
Built with Python, wordcloud, PyYAML, Pillow, NumPy, Matplotlib.
Cloud & Platforms
AI/LLMOps & Automation
CI/CD & Orchestration
Infrastructure as Code
Containers & Kubernetes
DataOps & Analytics
Security & Compliance
IAM & Access
Observability & AIOps
Programming
Testing & Reliability
Networking & Edge
Workflow & Low-Code Automation
Dashboards & Reporting
Legacy Modernization & Migration
Collaboration & Agile Delivery
Architecture & Governance
INL Home Run Award
Built a new Azure DevOps pipeline dashboard that gave leadership a high-level pipeline view and made outsized impact within weeks on site.
"Saved our Bacon" Team Award
Delivered nationwide debit card acceptance—integrated readers, refund logic, QA tooling, and production rollout on time and under budget.
Best Outgoing Consultant
Led “Special Projects” modernization assessments and trained global teams for regulated insurance programs.
Employee of the Quarter
Recognized for transforming legacy fraud systems and supporting enterprise-critical modern apps.
Cloud & GitOps Labs
Hands-on lab demonstrating AKS GitOps patterns with ArgoCD/Flux, IaC, and policy-first delivery for Kubernetes workloads.
DevSecOps Demos
Local CDC pipeline using MySQL, Debezium, Kafka, and a JDBC sink to replicate changes into Postgres with Kafka UI visibility, all via Docker Compose.
Vulnerable ASP.NET Core app (AspGoat-based) repurposed to showcase SAST/SCA pipelines with Snyk and SARIF reporting in GitHub Actions.
IaC and CI/CD security scanner with YAML rule packs, boxed console output, and an LLM-backed fix workflow for plan/apply remediation.
Snowflake & GenAI Actions
GitHub Action to invoke Snowflake CortexAI analyst workflows inside CI, enabling AI-assisted analysis on data assets during PRs.
GitHub Action wrapping CortexAI agent flows for automation and governance checks in pipelines.
GitHub Action to run CortexAI semantic search against Snowflake assets as part of PR validation.
GitHub Action to execute/validate SQL with AI assistance against Snowflake, supporting secure PR-time checks.
Lightweight GitHub Action for running Snowflake SQL in CI with parameterization and secrets hygiene.
TypeScript helper library that validates Snowflake configs and connection health for reuse across GitHub Actions.
Local CI workflows and scripts to validate action changes, run integration tests, and prep releases across Snowflake action repos.
Snowflake Tooling & IaC
End-to-end Snowflake IaC demo with Terraform: warehouses, databases, schemas, tables, views, dynamic tables, masking policies, tasks, stages, external/iceberg/hybrid tables, shares, and data loading patterns.
k9s-style terminal dashboard for Snowflake Snowpark Container Services (SPCS) with live service and compute pool status views.
- MBA - Technology and Financial Management
Contact
Let's build
Interested in DevSecOps, Data Engineering, DataOps, GenAI/LLMOps engagements?
Happy to discuss roadmaps, advisory, or hands-on delivery for CI/CD, DataOps, and AI-assisted governance with GenAI copilots.